Hack WiFi WEP/WPA2/+PSK Password Using Aircrack-ng
 Q. What happens if I have problems using the Super WiFi? Q. What occurs if I have problems using the WiFi Decoder? We recommend that you just watch the Video Guide and browse the Person Manual first earlier than utilizing the WiFi Decoder. First enter the command airplay-ng -1 zero -a 64:0F:28:6B:A9:B1 mon0 to carry out pretend authentication (-1 in command) to the network. I cannot join my Cetus 3d printer, which makes use of UP Studio’s software program, to my wifi network if there are space characters in my wifi password. Q. How can the WiFi Decoder find the password of a secured WiFi connection? Q. Can the WiFi Decoder affect my well being? 2. Now insert bootable the place you want to strive for hacking wifi password. Dictionary hack makes use of the dictionary for hacking the password, it tries all the mix of words out there in dictionary and if the password is combination of dictionary phrases, then this methodology is the best technique to hack any password. Then press F11 during rebooting and select Thumb Drive as Boot Up Drive.
Q. What happens if I have problems using the Super WiFi? Q. What occurs if I have problems using the WiFi Decoder? We recommend that you just watch the Video Guide and browse the Person Manual first earlier than utilizing the WiFi Decoder. First enter the command airplay-ng -1 zero -a 64:0F:28:6B:A9:B1 mon0 to carry out pretend authentication (-1 in command) to the network. I cannot join my Cetus 3d printer, which makes use of UP Studio’s software program, to my wifi network if there are space characters in my wifi password. Q. How can the WiFi Decoder find the password of a secured WiFi connection? Q. Can the WiFi Decoder affect my well being? 2. Now insert bootable the place you want to strive for hacking wifi password. Dictionary hack makes use of the dictionary for hacking the password, it tries all the mix of words out there in dictionary and if the password is combination of dictionary phrases, then this methodology is the best technique to hack any password. Then press F11 during rebooting and select Thumb Drive as Boot Up Drive.

Q. How to make use of USB Thumb Drive as well BT4 if my computer has no Disc Drive constructed-in? Q: Can I use the Super WiFi on my Notebook Computer? The WiFi Decoder is so highly effective that it may well receive WiFi connections up to 2 km away in open area! A. Sure. Most WiFi Adapter in a Notebook Computer are very low powered that has a variety of less than 20 meters. A. Yes, because the WiFi Decoder does not require an AC Adapter, It may be used in any place with a Pc or Laptop and normal WiFi connections, as WiFi requirements are the identical worldwide. Q. Can I be your agent? A. Please use the Agent Inquiry web page to contact us. BackTrack will ship a short help page. We’ll try to solve them for you ASAP. This time a client will present up, and wifite will de-authenticate it, and it will strive to attach once more. We’ll repair or change one for you and ship it again to you with free delivery.
- Wordlist of Kali Linux Password (Google IT)
- Begin machine and open Dolphin file manager
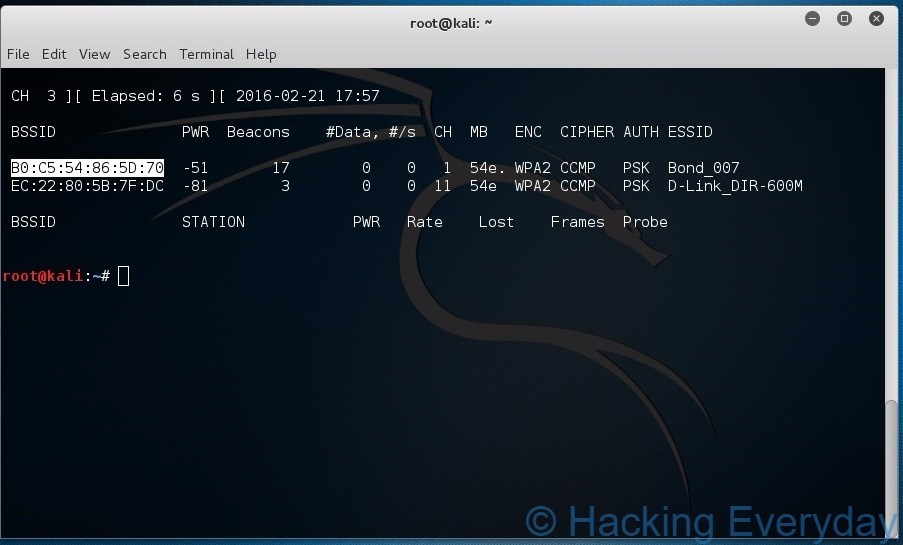
- Airodump-ng 1.2 rc2
- CommView for Wifi ( Download)
Q. Can I use the Decoder in a couple of pc at the same time? Nobody from gadgetcubes will take any form responsibility if something goes improper with you. Relying in your hardware pace and the size of your password checklist, this can take fairly some time to complete. Now there is not any direct manner of getting the password out of the hash, and thus hashing is a sturdy protection method. Now the captured handshake was saved as a .cap file which will be cracked utilizing aircrack, pyrit, hashcat (after changing .hccap), etc. using either a wordlist or bruteforce. So now it’s best to have a great understanding of the mask attack, right ? A very good WiFi connection can be shared by as much as 20 users or more. So After the Above Steps, We Should have the Handshake Packets and also We Should have WordList as we talked Above that you may Google That For latest WordList.
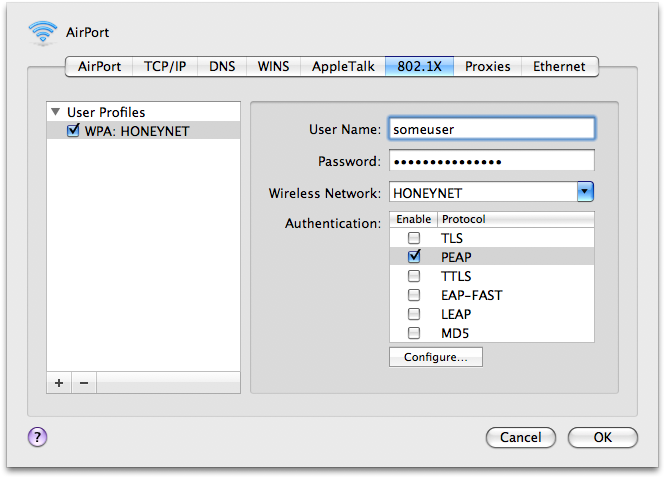
Deauth attacks send malicious deauthentication packets to the router you’re making an attempt to break into, inflicting the Web to disconnect and ask the Web user to log back in. If you’re using laptop computer, then it doesn’t require any further hardware. A. No, because the Decoder has to be plugged to a pc utilizing the USB Cable. Q. Can I use the WiFi Decoder on my Notebook Laptop? A. No, After you’ve decoded the passwords of the connections, simply write them down and you should use them for as long as you want, or till the administrator change the passwords. A. No, after you have got decoded the passwords of the connection, just write them down and you can use it for so long as you want, or till the administrator changes the passwords. Be taught what you’ll be able to. If anyone is already linked to the network, you possibly can test in his network properties to see what encryption-type is being using by the focused WiFi network. Instead, it’s carried out on the RSN IE (Sturdy Security Network Info Aspect) using a single EAPOL (Extensible Authentication Protocol over LAN) frame after requesting it from the access level.
This new WiFi hack method allows an attacker to retrieve the PSK login password (Pre-shared Key) to hack into WiFi community and sneak on Internet actions. After it makes the victim to connect with our Rogue WiFi Network and ask to replace Frimware by entering WiFi password. But, in some nation like Singapore, even if the network is unprotected and you utilize it without permissions yet get caught, you are still up for prosecution. A. In case you are using the WiFi Decoder by yourself connection or connections that are unencrypted then there are no authorized issues in any respect. Want know that find out how to hack wifi utilizing WiFiSlax. As early as 2001, proof-of-idea exploits had been floating around, and by 2005, the FBI gave a public demonstration (in an effort to extend consciousness of WEP’s weaknesses) where they cracked WEP passwords in minutes using freely out there software. And burn the BT4 software from CD to a USB Thumb Drive.