Study To Hack WIFI Password With Ubuntu (WPA/WPA2)
This will considerably scale back the quantity of potential passwords to include within the password dictionary. 10 Quantity of deauths to ship. This can take around 10 to 15 mins relying on your DVD Drive. As soon as the username and password have been accepted and you’re in the routers inside settings you may navigate to the security tab or administration tab relying on the particular brand of router that you’ve got. That is the main cause why Wi-Fi routers have become so vital since these units seem as an emblem of portability. Whether it is cell phone or laptop computer and even television gadget, all the pieces now comes with a built-in Wi-Fi router in order that we’re in a position to remain connected on a regular basis no matter the placement. The PMK performs an necessary part within the 4-method handshake that’s used to authenticate both the shopper and router known Pre-Shared Key (PSK) or the wireless password of the community.
- 7 Which Wordlist and Password record are you using in Kali Linux
- Straightforward to used not want special training
- Combinator assault
- Good person interface
- Sort: ./configure
 The PMK is part of the traditional 4-means handshake that’s used to confirm that both the router and client know the Pre-Shared Key (PSK), or wireless password, of the community. It’s a easy method for getting credentials from captive portals and third-celebration login pages (e.g. in social networks) or WPA/WPA2 pre-shared keys. This new WiFi hacking method could potentially permit attackers to retrieve pre-shared key (PSK) login passwords, permitting them to hack into your Wi-Fi community and communicate with the Internet. Nonetheless, this hacking tutorial is effective just for WPS enabled networks. Now find out whether or not target AP has WPS enabled or not. Instead, it’s carried out using a single EAPOL (Extensible Authentication Protocol over LAN) body on the RSN IE (Robust Safety Network Info Aspect) after requesting it from the access point. For a dictionary assault, we’ll want a wordlist which is everywhere in the internet. So this is how you hack a WPA/WPA2 network with dictionary attack.
The PMK is part of the traditional 4-means handshake that’s used to confirm that both the router and client know the Pre-Shared Key (PSK), or wireless password, of the community. It’s a easy method for getting credentials from captive portals and third-celebration login pages (e.g. in social networks) or WPA/WPA2 pre-shared keys. This new WiFi hacking method could potentially permit attackers to retrieve pre-shared key (PSK) login passwords, permitting them to hack into your Wi-Fi community and communicate with the Internet. Nonetheless, this hacking tutorial is effective just for WPS enabled networks. Now find out whether or not target AP has WPS enabled or not. Instead, it’s carried out using a single EAPOL (Extensible Authentication Protocol over LAN) body on the RSN IE (Robust Safety Network Info Aspect) after requesting it from the access point. For a dictionary assault, we’ll want a wordlist which is everywhere in the internet. So this is how you hack a WPA/WPA2 network with dictionary attack.
Hashcat can crack Wifi WPA/WPA2 passwords and you may as well use it to crack MD5, phpBB, MySQL and SHA1 passwords. Hashcat additionally has a rule-based engine. Be affected person, it would take a while. It could take a while for you to deauthenticate the consumer. I’ll present you easy methods to disconnect the client from the router. Let Me Show You ways.If You like The idea, Learn On And check out These Websites. Its a bit frustrating attempting it out. If you’re on the lookout for a faster way, I suggest you additionally take a look at my article on hacking WPA2-PSK passwords utilizing coWPAtty. For hacking the password, your wordlist must contain the precise phrase of the password. It is recommended that dwelling customers, who are very a lot prone to hack assaults and cybercrimes from a script kiddie or battle driver, must use WPA-PSK methodology for securing their wireless network. In most cases, the wireless community interface title is “wlan0”.
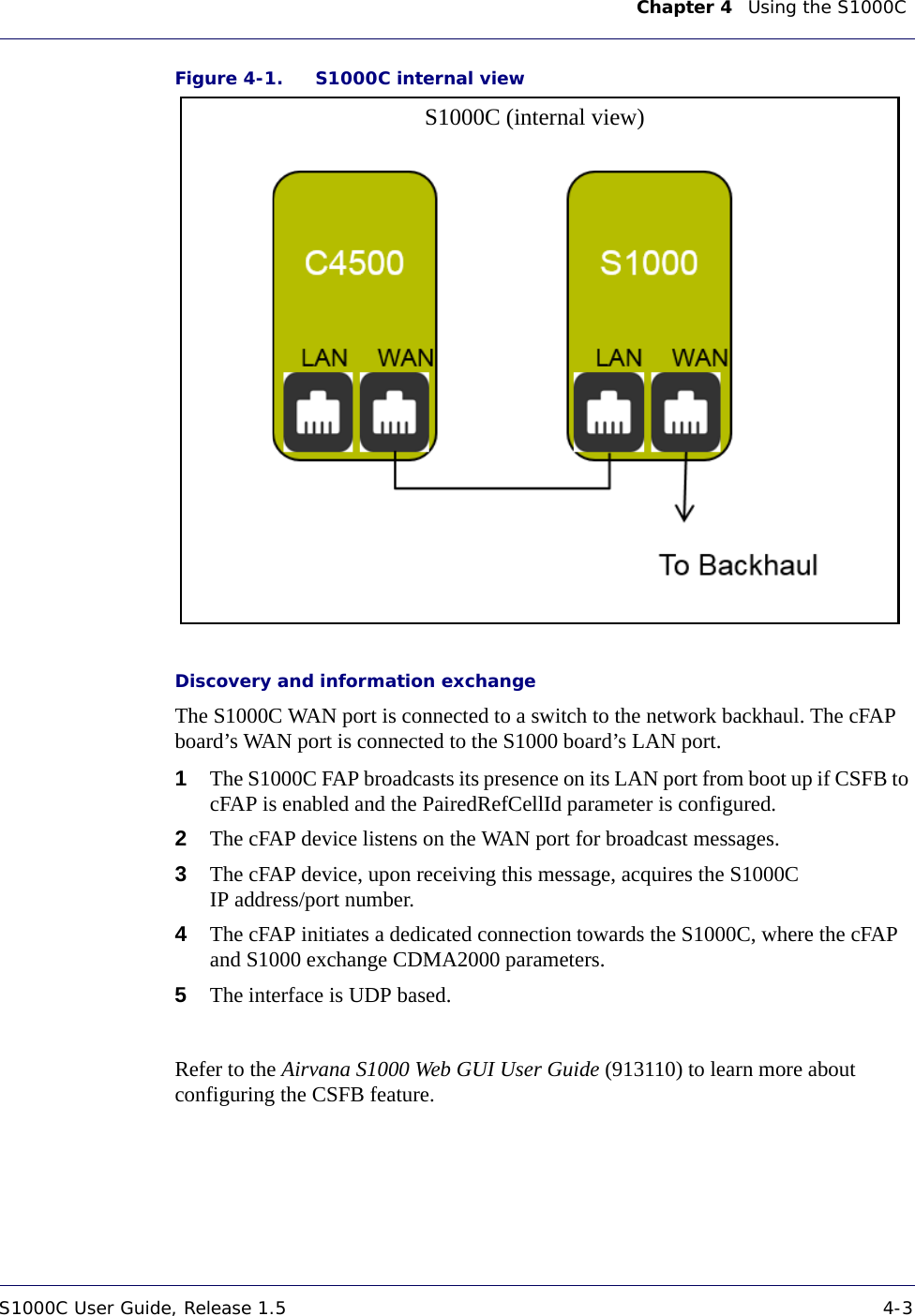
Word the title of your wireless interface. Want a wireless community adapter? Now, in this case, a easy adapter like WN722N would be enough the produce the PMKID. Now, here’s little unhappy part. Packet injection means interfering with other networks via constructing packets to seem as if they are a part of the conventional communication stream. The network adapter ought to be capable of packet injection. All it’s good to know is if your community adapter is able to injecting packets or not. There is a listing of Community Adapters which are suitable with Backtrack and able to injecting packets. It takes around 4 to 10 hours to hack the community. Typically it takes just a little time for the station to point out up. After you hit the download button, the above page will show up. It will present many informations about the entry level. Keep looking out until your sufferer (your targeted entry point) appears.