Hacking WPA/WPA2 Wi-fi With Hashcat Full Tutorial 2020
Open up your Command Prompt/Terminal and navigate your location to the folder that you just unzipped. Enter the following code, ensuring to exchange the mandatory parts of the command with your network’s data: airodump-ng -c channel —bssid MAC -w /root/Desktop/ mon0- Exchange “channel” with the channel quantity you discovered in the last step. Turn on airmon-ng. Type in the next command, then press ↵ Enter. A wireless community password is usually required to attach a printer or different sort of wireless device to your wireless community. That’s the password of your targeted wireless network which can take time to crack depending on its size or size complexity. We are diving you particulars about three useful software program that can teach you the right way to hack WiFi password Crack Wireless. The RSN protocol permits you to ascertain safe communications over 802.Eleven wireless networks. This may listing the wireless card properties related to your laptop that helps monitor mode. This command will show the hardware properties of your laptop.
 Now, to make use of this key, firstly start the processes you have got killed in Step 1 above using the command I have used beneath. Subsequent step is vital to See all the things about your target community BSSID is mac handle ESSID is the name of Network. Exchange “MAC” with the MAC tackle you discovered in the last step. BSSID is the bodily handle of that router. You want to seize the BSSID of the target wifi or router. Copy the BSSID of the wifi that you simply need to hack or crack. Find the router you wish to hack. Click HTTP subsequent to the version of Kali you need to make use of. All you have to do is to click on the circular arrow button situated at the best-hand facet of the password field. 2. Within the Class list, click on Passwords. Users have to be skilled and educated concerning the importance of not reusing passwords.
Now, to make use of this key, firstly start the processes you have got killed in Step 1 above using the command I have used beneath. Subsequent step is vital to See all the things about your target community BSSID is mac handle ESSID is the name of Network. Exchange “MAC” with the MAC tackle you discovered in the last step. BSSID is the bodily handle of that router. You want to seize the BSSID of the target wifi or router. Copy the BSSID of the wifi that you simply need to hack or crack. Find the router you wish to hack. Click HTTP subsequent to the version of Kali you need to make use of. All you have to do is to click on the circular arrow button situated at the best-hand facet of the password field. 2. Within the Class list, click on Passwords. Users have to be skilled and educated concerning the importance of not reusing passwords.
- Kali 2 & 2016 help the newest Aircrack-ng versions
- 6 How to stop Dictionary Attacks
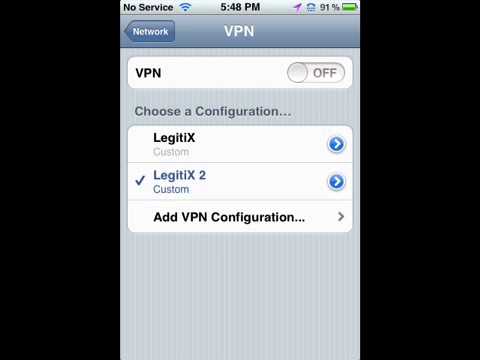
- Activate the VPN
- Flip In your monitor interface by typing the beneath command
- U retrieve usernames from WiFi-traffic
If you’re utilizing Kali Linux in a virtual machine, you will have a Wi-Fi card no matter your computer’s card. I’m sure that I am inputting the proper password (it is the WPA2 password written on the router; it isn’t the wi-fi password itself), and it keeps getting rejected. Ensure the router is utilizing WPA or WPA2 safety. You possibly can easily decrypt all kinds of encryption reminiscent of WEP, WPA and WPA2. Once a password has been imported, we can run a batch command to create a DB. Above command will enable monitor mode. In my case, it’s eight look it above screenshot. In my case, that’s wlan0. Exit airodump-ng, then open the desktop. Open up terminal window from your linux desktop. While in the second method i’ll use phrase list technique in this kali linux wifi hack tutorial. Your search ends here, here in the present day i’ll present you two methods by which you’ll be capable to hack wifi using kali linux.
I used to be ready to attach my printer to the identical router hardware on its guest community using a WPA2 password without areas. All of us of us enable auto-connect with our community. The community password is likely to be weak and really straightforward to interrupt, however without a machine connected to briefly kick off, there is no opportunity to capture a handshake, thus no likelihood to strive cracking it. When any machine disconnects from the router, you will notice WPA Handshake captured in the earlier terminal. Using following command you possibly can seize WPA handshake. Now enter the following command – “ifconfig” and hit enter. Basically now you need to notice down or copy the tackle listed below Interface. Enter your root username and password when logging in.- You’ll must be on your root account always throughout the hacking course of. 1. Close pointless tabs it can create process fast. It would continue until you didn’t cease it. Generally, merely attaching the card to your pc will be sufficient to set it up. I set up my userid and password, does AT&T Laptop having a headache. As soon as any user enters the WiFi password, voila, you now have the password.
Now again you’re going to get a brand new monitor interface property name just right under the Interface choice. Now half 1 is full return to your private home. Deauth assaults ship malicious deauthentication packets to the router you’re trying to interrupt into, inflicting the Internet to disconnect and ask the Web user to log again in. Most of the modern routers are secured from all forms of assaults. “At this time, we have no idea for which vendors or for what number of routers this technique will work, but we think it’s going to work towards all 802.11i/p/q/r networks with roaming features enabled (most trendy routers),” Steube added. Inform your pc to hearken to close by routers. A “handshake” happens when an item connects to a network (e.g., when your laptop connects to a router). 2. Use A couple of Laptop with completely different phrase checklist recordsdata. For example, we will use Crunch in Pyrit with pipeline. An inventory of all the security encryptions available to you may be viewed by clicking the downward arrow button situated at the appropriate-hand aspect of the kind option.