How To Hack WiFi Password Simply Utilizing New Attack On WPA/WPA2?
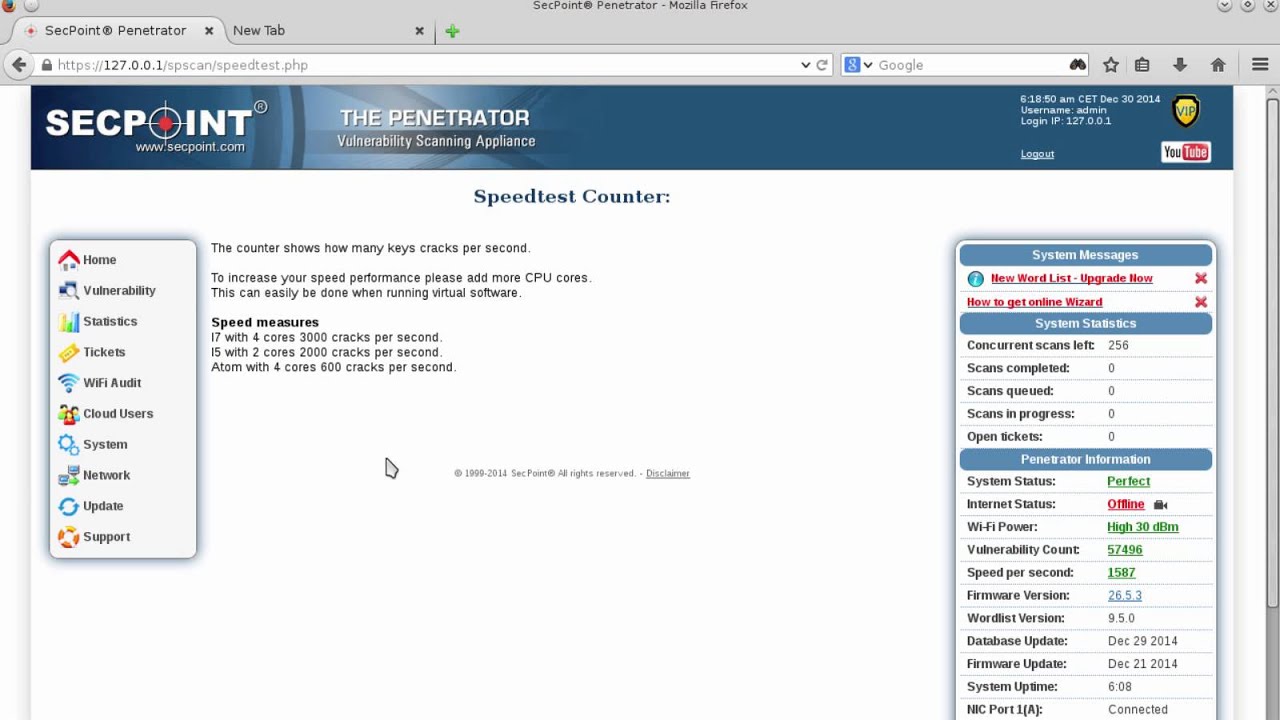
Together with the Dutch National Cyber Security Centre we now have initiated a responsible disclosure process. Moreover, we describe a process that may instantly collect an entire wireless authentication hint which permits an offline password recovery attack. Use the next command to import previously created password dictionary wpa.lst to Pyrit Database. Finally, lets rename this file to wpa.lst. So let’s make our cowpatty file. Learn to Make Use Of these WIFI Networks That are Laying Idle Round You Waiting So that you can Harness Them! I’ve created a particular MASK file to make issues faster. Rainbow tables are recognized to speed things up, by finishing a part of the guessing job beforehand, but the output rainbow desk that must be downloaded from the online is disastrously giant (might be 100s of GBs typically). Put together your right instruments for the job. Personally, I feel there’s no proper or fallacious way of pentesting a Wireless Entry Level.
It is best to create your individual MASK file in similar means I explained earlier. Hashcat picks up phrases one after the other and test them to the every password doable by the Mask defined. Once a matching password is discovered in the dictionary file, the cracking process will stop with an output containing the password. That’s it. It would take few minutes to undergo the entire Database Table to get the password if it existed in the Dictionary. Fluxion works through the use of something like a man in the center assault/ evil twin attack to get WPA password instead of going the bruteforce/dictionary route. This may keep going until the end of the file. Observe: cowpatty will fail in case your password/dictionary file is larger than 2GB. You’ll should follow airolib-ng although that’s slower. Awesome, now we have our ESSID added to Pyrit Database. That is due to the fact that most of the networks that at the moment are secured in the present day are achieved below the WPA2 safety expertise. But this is very troublesome, as a result of WPA/WPA2 is an excellent security.
- 1 * 1 WPA 99db no shopper
- Kali Linux 2 or Kali 2016.1 rolling or
- Monitor Mode (airmon-ng)
- A three is the Attack mode, custom-character set (Mask assault)
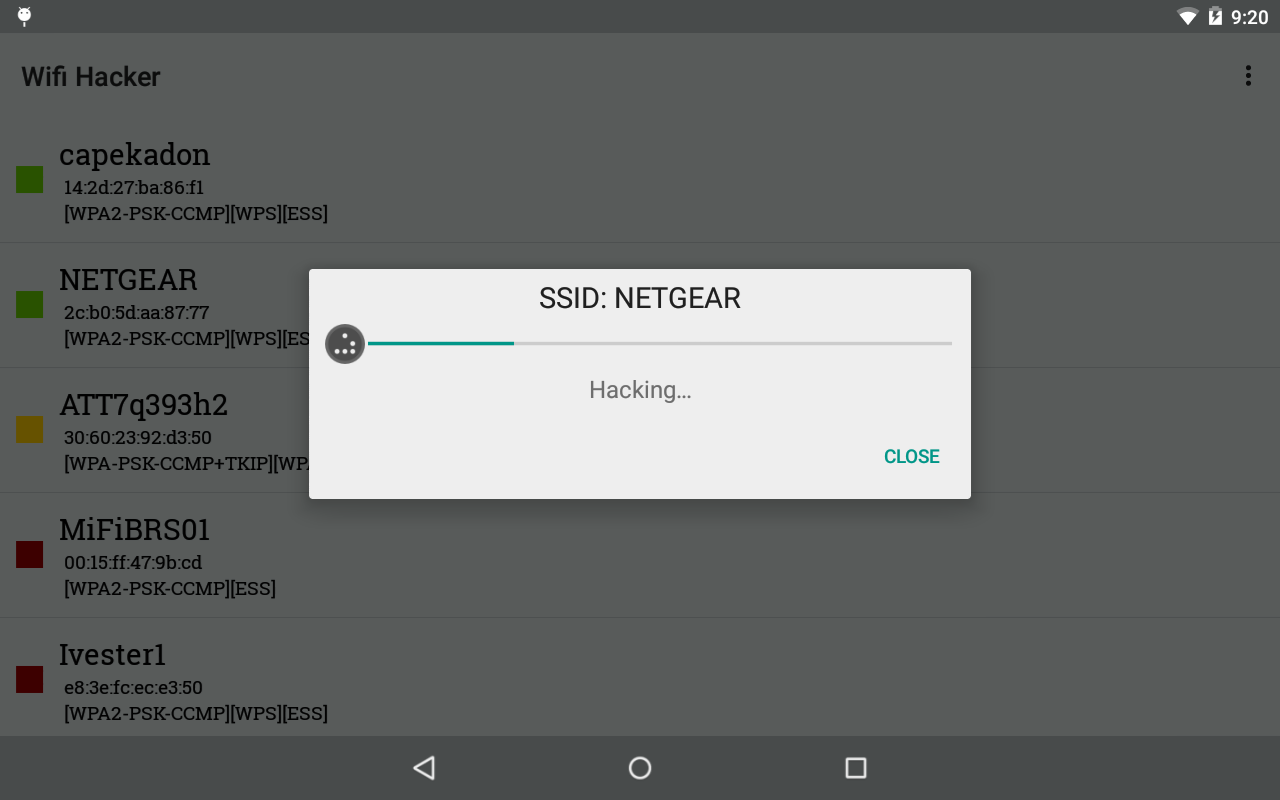
- This device has a consumer-friendly interface
Fluxion script has been out there for some time and is most apt for safety researchers and pentesters to check their network security by hacking WPA/WPA2 safety without brute forcing it. It is understood that WEP will be hacked by brute power – to this point solely only a few circumstances of harm by way of malicious hacking of WEP are known. So we’re saving this file as newrockyou.txt name. Let’s copy one in every of best dictionary file to root listing. As a result of WPA2 minimum password requirement is eight characters, let’s parse this file to filter out any passwords that is lower than 8 characters and greater than sixty three characters. Learn how to recuperate your Windows password and in addition crack Wifi Passwords on Home windows 7/XP/eight and eight The way to crack wpa2-psk wifi password in windows. I from a village so there is only one wifi community accessible. If you happen to discover that IVS worth will not be running, or operating very very gradual after few minutes, it signifies that there is no knowledge switch on the router.
Which means this password is all in numbers. That’s 14344392 passwords. So we made this file shorter which suggests we are able to test extra AP’s in less time. Thanks for reading. This process just isn’t at all times possible and generally cracking Wifi WPA/WPA2 passwords using Reaver-WPS is much easier. What’s the perfect technique to hack a WiFi community secured with WPA/WPA2 PSK, get its password, .Find out how to Crack WPA / WPA2 – SmallNetBuilder . It is simpler than you think, so let’s get to it! Let’s dig a bit deeper now. Now that we’ve our cowpatty output, let’s try to crack WPA2/PSK passphrase. Wikipedia, for example, lists a collection of security flaws that have been recognized since WPA2 was launched in September 2004. The most high profile, perhaps, was the important thing Reinstallation Attack, or KRACK attack, identified final 12 months. Now that we have our ESSID added to Pyrit database, lets go an import our Password Dictionary.
And bingo, it found a matching password. You might be able to find the wireless community password from a computer that’s connected to the wireless network. Q. How to use USB Thumb Drive to boot BT4 if my computer has no Disc Drive built-in? Fluxion shouldn’t be a lot totally different from Linset but makes use of sure improvements, bug fixes, and extra features. Fluxion relies on one other script called linset. Fluxion is compatible with the latest release of Kali (Rolling). Newest builds (stable) and (beta) right here. Simply kind the following to put in the most recent version of Hashcat. It will be in the same directory you’ve ran Hashcat or cudaHashcat or oclHashcat. Airodump-ng will now monitor all the wireless networks available in your area. Now open Elcomsoft Wireless Security Auditor to crack your wifi password. The key with safety bugs is to be able to react rapidly and appropriately. In order to correctly protect your wireless network it is important to create your individual key reasonably than using the one generated by the router. First Run hcxdumptool to achieve the PMKID from the AP and dump the file in PCAP format utilizing following code. To crack utilizing cowpatty, you need to export in cowpatty format after which start the cracking process.