Hack WiFi: The Right Way To Crack WPA/WPA2 With PMKID Assault (WiFiBroot)
 Let’s say, we somehow got here to know a part of the password. Sufficient with the warnings – Let’s Soar into the main usage. Researchers have found a new and apparently very easy method to crack WPA/WPA2 PSK enabled Wi-Fi networks. How do hackers and crackers break WiFi encryption for WEP WPA WPA2 WPS Keys in a straightforward manner with software program? After it makes the sufferer to attach with our Rogue WiFi Network and ask to replace Frimware by coming into WiFi password. Although breaking into a WPA/WPA2 secured network utilizing this vulnerability requires wherever from 2-14 hours of sustained effort with a trendy pc, it remains to be a respectable safety concern. It’s accessed through your browser and requires no special browser extensions or plug-ins to function. This particular software was developed to reveal password of protected Wi-Fi networks. It’s a easy technique for getting credentials from captive portals and third-social gathering login pages (e.g. in social networks) or WPA/WPA2 pre-shared keys.
Let’s say, we somehow got here to know a part of the password. Sufficient with the warnings – Let’s Soar into the main usage. Researchers have found a new and apparently very easy method to crack WPA/WPA2 PSK enabled Wi-Fi networks. How do hackers and crackers break WiFi encryption for WEP WPA WPA2 WPS Keys in a straightforward manner with software program? After it makes the sufferer to attach with our Rogue WiFi Network and ask to replace Frimware by coming into WiFi password. Although breaking into a WPA/WPA2 secured network utilizing this vulnerability requires wherever from 2-14 hours of sustained effort with a trendy pc, it remains to be a respectable safety concern. It’s accessed through your browser and requires no special browser extensions or plug-ins to function. This particular software was developed to reveal password of protected Wi-Fi networks. It’s a easy technique for getting credentials from captive portals and third-social gathering login pages (e.g. in social networks) or WPA/WPA2 pre-shared keys.
- Wireless Broad Space Community
- One thing improper with wireless card
- Brute-Drive attack
- Professionals arrange a further separate community
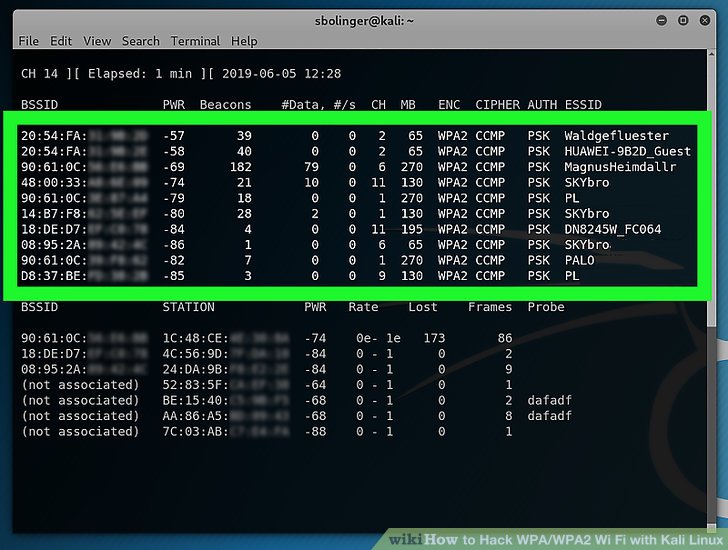
WPS stands for “Wi-Fi Protected Setup however this abbreviation is not the original, in fact, WPS is originally Wi-Fi Easy Config. Keep one thing in mind that – this is a simple methodology to exploit the weakest hyperlink within the consumer server hyperlink – i.e. the person. This methodology can be there and may fit even. Now a new popup will seem titled as “Wi-Fi Status” there in the general tab click on the Wireless properties option. Under WPS tab click on on the select all networks, by doing so all of the networks which have enabled WPS can be listed. For those who do a full packet seize, you will be capable to search for the reassociation packets in the capture to verify deauthentication labored. So, Simply have a brief look on the steps and methods & instruments that we gonna use here. So, that is why we gonna use this superb creation within the open source community to Crack Wifi password without any Software. Nonetheless, it differs from other WiFi hacking methods; this assault does not require capturing a 4-manner LAN Extensible Authentication Protocol (EAPOL) authentication handshake. One of the most significant adjustments between WPA and WPA2 is the obligatory use of AES algorithms and the introduction of CCMP (Counter Cipher Mode with Block Chaining Message Authentication Code Protocol) as a alternative for TKIP.
WPA – WiFi Protected Entry (WPA) is improved and extra secured safety protocol which arrived with numerous enhancements in encryption and authentication methods of WEP. Step 3- To get the WPA PSK (Pre-Shared Key) password, use Hashcat (v4.2.0 or greater) password cracking instrument, and bingo, that’s easy methods to hack the wifi password. It is very advisable to not use this technique in any of the unlawful activities. It was one of many fantasies of mine to know such technique which does precisely what we gonna do here in this text. This methodology is probably the most simplest and probably the most straightforward for all sort of people who want to turn into a hacker. Wifi password hacking has turn into common as individuals are always searching for the free web. 1 Crack WPA/WPA2 Wifi Password utilizing Fluxion1.1 What’s Fluxion? When you’ve got any problem while downloading any software program then you may contact me using the contact type or drop a remark. Clicking on the JumpStart button will begin the jumpstart providers and that may begin hacking your desired password utilizing PIN assault system.
1. Close unnecessary tabs it should create course of quick. I’ve seen many young’s which desires to change into an knowledgeable hacker but they can’t however don’t worry I’ll guide you throughout the strategy of studying hacking and grow to be a profitable hacker. When you miss anyone of the software from there them the Hacking course of can’t be complete so watch out while putting in the entire software program on your laptop. The Krack security exploit was found by Mathy Vanhoef, a cybersecurity professional at Belgian college KU Leuven, who will present his research at the pc and Communications Security (CCS) conference later this month. Now, there can be some people in the business who will use this to try to discredit WiFi as an insecure know-how. The software program helps a stunning array of formats (not simply Wifi passwords from WPA/WPA2 handshakes), supplies unique search controls, and presents unmatched restoration speeds on any trendy computer.
The United States Computer Emergency Readiness Group (US-CERT) has issued an alert about Russian state-supported hackers finishing up assaults against numerous residence routers in the U.S. Having stated that, we, of course, are aware and alert about this. If you are on the Pen-take a look at path you want a Pen-check OS Like Backtrack. Kali Linux, BackTrack 5 and so on. And, it has most of the tools it’s essential crack a wireless community. And, a bit technical. And, should you do so – solely you’ll be chargeable for such actions. Any actions and or activities associated to the material contained inside this Web site is solely your responsibility.The misuse of the knowledge on this web site can lead to criminal expenses introduced towards the individuals in query. Again, the result of this little trick is smart, however it is not environment friendly. Here we’re sharing this on your academic goal. This text is just for an educational goal. It then creates a villain wireless entry goal that’s shapely by the target. Additionally, it sniffs the realm and copies the goal access point’s settings. Depending upon your target you’ve gotten to change channel number.