WPA/WPA2 Wifi HACKING PASSKEY Recovery MADE Simple . 7 MOST Powerful WIFI APPS COMPILATION
Its an Authentication Process to allow the Shopper to be related to the Access Point. Stations are the Computers/Sensible Phones or any Wireless Gadgets at the moment related to the BSSID they are Related to. 1. WPA and WPA2 safety carried out without utilizing the Wi-Fi Protected Setup (WPS) function are unaffected by the safety vulnerability. That is the characteristic I used to be talking about. You do this by establishing a totally completely different Wi-Fi router or enabling your router’s “Guest Community” possibility, a preferred characteristic for many routers. Wi-Fi Protected Entry (WPA) was the Wi-Fi Alliance’s direct response and alternative to the more and more obvious vulnerabilities of the WEP customary. As a result of factors comparable to information dependant branching, serialization, and Reminiscence (to name just a few), oclHashcat is just not a catchall alternative for Hashcat. Our Wireless Interface “mon0” will now capture Packets only from Channel 1 from a specific BSSID and write all the info to a File referred to as “wep.ivs”. Should you didn’t receive the “handshake message,” then one thing went improper within the process of sending the packets.
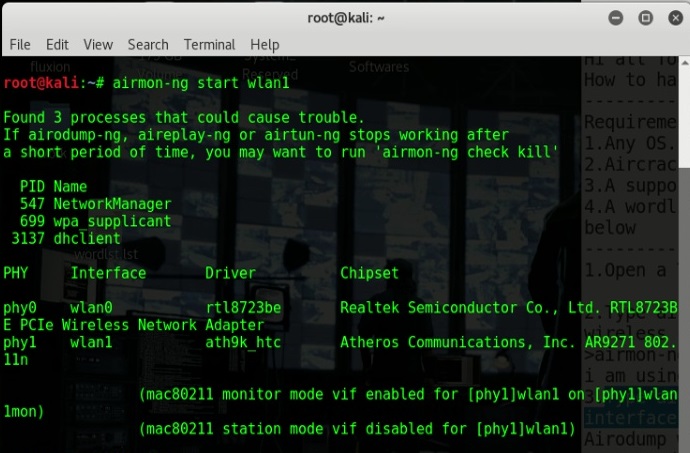
 In this text, I will explain methods to crack WPA/WPA2 passwords by capturing handshakes, then utilizing a phrase record, to crack the password protected the entry point. Then your ready if you attempt for real. As you can see in the above Picture, My Wireless Card Exhibits up as “wlan0”. In case you are Utilizing a Boot CD, As in my case, You will see the folllowing display screen when the CD Hundreds. Since, In this case, We have already got a Station related to the Community. In my case, it’s eight look it above screenshot. That is what it may seem like in case your Wireless Interface is Efficiently put into Monitor Mode. Now, We have now taken care of What Our Target Should seem like. And in case you do not have already got Backtrack, I recommend you bookmark this web page and get it first. It’s broadly preferred for password protection and usually the first choice for users who require router configuration tools. But in this text, we will dive in in another device – Hashcat, is the self-proclaimed world’s quickest password restoration device.
In this text, I will explain methods to crack WPA/WPA2 passwords by capturing handshakes, then utilizing a phrase record, to crack the password protected the entry point. Then your ready if you attempt for real. As you can see in the above Picture, My Wireless Card Exhibits up as “wlan0”. In case you are Utilizing a Boot CD, As in my case, You will see the folllowing display screen when the CD Hundreds. Since, In this case, We have already got a Station related to the Community. In my case, it’s eight look it above screenshot. That is what it may seem like in case your Wireless Interface is Efficiently put into Monitor Mode. Now, We have now taken care of What Our Target Should seem like. And in case you do not have already got Backtrack, I recommend you bookmark this web page and get it first. It’s broadly preferred for password protection and usually the first choice for users who require router configuration tools. But in this text, we will dive in in another device – Hashcat, is the self-proclaimed world’s quickest password restoration device.
I believe that can be totally inappropriate; it’s an unfortunate flaw in a typical, it’s been identified, and can be mounted quickly. So, even in quickest computer you may manage to make use of, it’s going to take hours. They might be capable to get entry to any unencrypted visitors between the machine and the entry point and even decrypt WiFi. The purpose in a De-Authentication Attack is to Forcefully De-Authenticate a Certain or All Stations from an Access Level. While Stations usually are not essential to crack a WEP Encrypted Network, Stations are a must should crack a WPA/WPA2 Protected Community. You will need to have Noticed, The Column of Stations. Now I don’t dwell in a metropolis, I dwell within the suburbs of Bergen county NJ the place I produce other one household houses round me. Now that we’re Prepared.. If you are trying to recover it.. A Dictionary that has the Password we are attempting to get.
- Airmon-ng begin wlan1
- Copy and paste reaver-1.4.tar.gz into the folder “root” as proven in the picture under
- Don’t use public WiFi networks unless it’s obligatory
- Kind http://192.168.2.1 within the handle bar and press Enter
- Wireless Metropolitan Area Networks
- 5 blockchain-based mostly messaging apps for full anonymity on iOS and Android
- Does it have WPS enabled. If not, then the attack will not work
 Which is able to allow us to Seize the Handshake and Initiate a Dictionary Assault. In WPA/WPA2, We have to get a Handshake in order to be able to Initiate a Dictionary Assault aganist that Community. To Do a Dictionary Assault, You need a WPA Handshake. To Get WPA Password, That you must do a Dictionary Attack. To stop unauthorized utilization of the sources available on a Wi-Fi router, numerous varieties of password safety strategies are being utilized for example WEP, WPA and WPA-PSK. There are some details in there too. Before we Scan for WPA/WPA2 Networks, There is one thing I need to make a remark of right here. On this Mode, Fairly Simply, We will probably be ready to monitor all of the Visitors that flows round in our Scan Space. Next, we’ll put our card into wireless monitor mode with the command airmon-ng begin wlan1. Now, We are going to put the Wireless Card into Monitor Mode. With the assistance of hcxpcaptool software, the outcome of the frame will probably be transformed right into a hash format admitted by Hashcat. Hashcat or oclHashcat or Hashcat on Kali Linux got constructed-in capabilities to assault and decrypt or Cracking WPA2 WPA with Hashcat – handshake .cap files.
Which is able to allow us to Seize the Handshake and Initiate a Dictionary Assault. In WPA/WPA2, We have to get a Handshake in order to be able to Initiate a Dictionary Assault aganist that Community. To Do a Dictionary Assault, You need a WPA Handshake. To Get WPA Password, That you must do a Dictionary Attack. To stop unauthorized utilization of the sources available on a Wi-Fi router, numerous varieties of password safety strategies are being utilized for example WEP, WPA and WPA-PSK. There are some details in there too. Before we Scan for WPA/WPA2 Networks, There is one thing I need to make a remark of right here. On this Mode, Fairly Simply, We will probably be ready to monitor all of the Visitors that flows round in our Scan Space. Next, we’ll put our card into wireless monitor mode with the command airmon-ng begin wlan1. Now, We are going to put the Wireless Card into Monitor Mode. With the assistance of hcxpcaptool software, the outcome of the frame will probably be transformed right into a hash format admitted by Hashcat. Hashcat or oclHashcat or Hashcat on Kali Linux got constructed-in capabilities to assault and decrypt or Cracking WPA2 WPA with Hashcat – handshake .cap files.
WPA/WPA2 has been dwindling after the discovery of WPA2 key-reinstallation assault (KRACK) and whereas testing the new WPA3 protocol, Jens Steube stumbled upon on one other vulnerability in WPA2 protocol, rejecting the need for a handshake to be in place. Cracking WPA2 WPA with Hashcat in Kali Linux (BruteForce MASK based mostly assault on Wifi passwords) new ! What you are Seeing is A listing of All the WPA/WPA2 Encrypted WIFI Networks round you. In case you’re undecided, Use the Take a look at Mode in Aireplay-ng (-9) to see if it supports packet Injection. Step 9: Listed below are the wps enabled networks out there around me :p. 5. Now keep on the identical page, choose All Networks from the top and hit Scan. A captive portal is launched as a way to serve a web page, which prompts the user to enter their WPA password. And So as to get this Handshake, We have to De-Authenticate a Linked Consumer (Station).