New Method Makes Hacking WPA/WPA2 Even Simpler
 Here I have NVidia’s graphics card so I take advantage of CudaHashcat command adopted by 64, as I am utilizing Home windows 10 64-bit version. I’M GOING To supply THE Frequent METHODOLOGY That is Adopted WHEN HACKING A MACHINE/Network/SERVER. But we’re not likely going to look forward to a device to attach, no, that’s not what impatient hackers do. Whereas the brand new assault against Wi-Fi passwords makes it easier for hackers to try an attack on a goal, the same strategies that were efficient in opposition to earlier kinds of WPA cracking stay efficient. If you take a look at the opposite terminal, we now have profitable captured the WPA handshake. It may possibly perform 4-manner handshake by disconnecting/connecting the connected machine and capturing WPA handshake. If you happen to see mon0 link then you may continue, ( However perhaps instead of mon0 you’ll be able to have another title ) if no then repeat previous steps. It’s then after these requests that the access level dispatch the primary EAPOL body which comprises the PMKID in RSN layer.
Here I have NVidia’s graphics card so I take advantage of CudaHashcat command adopted by 64, as I am utilizing Home windows 10 64-bit version. I’M GOING To supply THE Frequent METHODOLOGY That is Adopted WHEN HACKING A MACHINE/Network/SERVER. But we’re not likely going to look forward to a device to attach, no, that’s not what impatient hackers do. Whereas the brand new assault against Wi-Fi passwords makes it easier for hackers to try an attack on a goal, the same strategies that were efficient in opposition to earlier kinds of WPA cracking stay efficient. If you take a look at the opposite terminal, we now have profitable captured the WPA handshake. It may possibly perform 4-manner handshake by disconnecting/connecting the connected machine and capturing WPA handshake. If you happen to see mon0 link then you may continue, ( However perhaps instead of mon0 you’ll be able to have another title ) if no then repeat previous steps. It’s then after these requests that the access level dispatch the primary EAPOL body which comprises the PMKID in RSN layer.
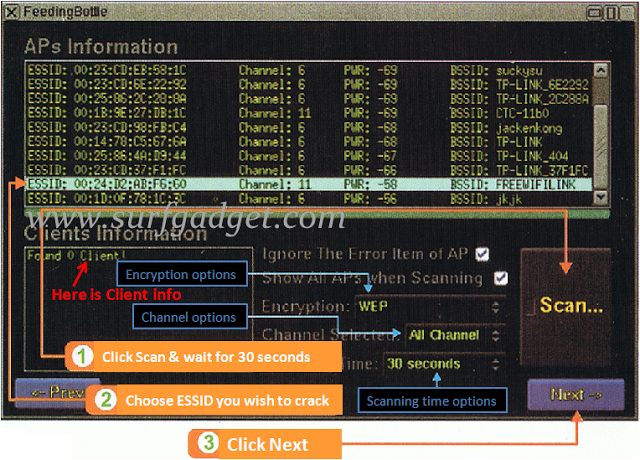
The RSN IE is a optional field that incorporates the Pairwise Master Key Identifier (PMKID) generated by a router when a user tries to authenticate. Found by the lead developer of the favored password-cracking software Hashcat, Jens ‘Atom’ Steube, the brand new WiFi hack works explicitly against WPA/WPA2 wireless network protocols with Pairwise Master Key Identifier (PMKID)-based roaming features enabled. You want the Aircrack-ng suite (in Kali Linux, it comes as a constructed-in instrument). So it presents an arsenal tool for WiFi safety and for auditor. Hack any community safety. The brand new attack is made on the RSN IE (Sturdy Security Network Data Component) of a single EAPOL frame. EAPOL frames start as successors to Authentication and Association requests. 1. After downloading please burn into USB Flash drive with Rufus USB Burner. Bootable file just burn into USB and used. After making bootable you might want to insert where you wish to hacking password and run your system or boot your system on Beini Bootable USB or CD. Intention: To crack a WPA2-psk encrypted WiFi password using Aircrack-ng.
In earlier submit we learn to hack WEP encrypted WiFi password. In case you have any questions on this tutorial on Wi-Fi password cracking or you have a remark, be at liberty to succeed in me on Twitter @KodyKinzie. It should let you employ the internet almost everywhere at no cost thereby saving you hefty monthly subscription charges. This is where hcxtools differs from Besside-ng, in that a conversion step is required in order to organize the file for Hashcat to use. 4. From the step 3 above, we are able to find access point with encryption algorithm WPA2 and observe the AP channel quantity. WPACRACK10-01.ivs is a file title we give it on step six. THIS TUTORIAL Provides you with An excellent UNDERSTANDING & An outline ABOUT Professional PENETRATION Test IN A BLACK Box (ATTACKER) Standpoint. It takes observe. What worked for me is hack my own router till I received good at it.
- Set your wireless interface in monitor mode-
- W path to phrase checklist in my case it’s ‘/root/Desktop/wordlist.txt’
- The length of the password matters rather a lot, it is an effective defence in opposition to brute-power attacks
- Activate and take a look at the firewall
- 1 ************** me WPA (1 handshake)
- Right-click on on the community you simply joined and hit ‘Properties’
- sixteen bytes of EAPOL-Key Confirmation Key (KCK)- Used to compute MIC on WPA EAPOL Key message
So, you do not must reset your Wifi router or pay additional cash for someone that can assist you reset or re-configure your access point at your house or office. The wireless password (or WPA2 password the MAC refers to) is on the bottom half of the router label. WPA2 has been around for greater than 6 years and WPA2 hacking/cracking is often gradual because it has to look forward to a client to auth or deauth earlier than cracking it. Not too long ago, this idea emerged of cracking WPA2 in cloud servers. Mainly, Hashcat is a method that makes use of the graphics card to brute force a password hash as an alternative of utilizing your CPU, it is quick and extremely versatile- to author made it in such a approach that enables distributed cracking. Now its begin password cracking process. Best of all it may also decode, hack, crack, unlock and reveal the passwords of many of the secured connections for those who overlook your individual password. Although WPS is marketed as being a safe way of configuring a wireless gadget, there are design and implementation flaws which enable an attacker to gain entry to an in any other case sufficiently secured wireless network.
WiFi alerts are available nearly in every single place however most of them are ineffective to us as they are is likely to be too far away from your home to entry. ANYHOW, IT May be Helpful FOR INTERMEDIATE/Consultants TOO! The gadget you’re trying to deauth may not be set to routinely reconnect, wherein case you’ll both should try another machine, or go away airodump on indefinitely until someone or something connects to the community. If you’re using a Kali Linux in VMware or different virtual machines, then it is advisable get a suitable USB WiFi receiver (I’m using an Atheros AR9271 wireless network adapter), as a result of WiFi connections don’t present up in virtual machines. Should you dual-booted your system and/or using Ubuntu or Mint Linux, then you’re good to go. Good Query, Properly the reply is very simple. It’s a easy technique for getting credentials from captive portals and third-social gathering login pages (e.g. in social networks) or WPA/WPA2 pre-shared keys. And with Passcovery’s simple person interface (choose between the clear graphic interface and the minimalist command line interface), it’s easy to restoration WiFi passwords.