Cracking Wifi WPA/WPA2 Passwords Using Pyrit Cowpatty In Kali Linux
Reaver has a known issue : Typically it doesn’t work with Virtual Machines, and you might should do a dwell boot using stay CD or reside USB of Kali Linux. If not, then the attack is not going to work. Now to test whether or not the network has WPS enabled or not, you’ll be able to both use wash or simply use the good old airodump-ng. Wash is specifically meant to verify whether a network has WPS enabled or not, and thereby is far simpler to use. Now principally it was meant to make WPA even more durable to crack, and much simpler to configure (push a button on router and gadget connects). This make the task a billion billion instances more durable. This task will be simply achieved using pixiewps. This tutorial explains a significant safety flaw in WPS enabled routers, if discovered susceptible the password protection will be bypassed inside seconds as defined in tutorial. “This assault variant was discovered incidentally while we had been wanting for methods to attack the brand new WPA3 safety commonplace.
- Proper-click on the identify of your wireless network, and then click on Standing
- one hundred is the number of de-authenticate frames you need to send
- Linux working system
- Now we use wifite for capturing the .cap file that contains the password file
- Kali Linux 2 or Kali 2016.1 rolling or
- After ending restart your Laptop and boot it from your USB
- Bssid : MAC deal with of the target AP
 So, test the record of routers vulnerable to this attack accessible on google and cease utilizing WPS if your router is listed there. So, where is this taking us? So, they came up with a superb solution which no different password restoration device presents built-in at this second. Choose a file with “.cap”extension and kind the following command “aircrack-ng -w ” (aircrack-ng is a software that helps in cracking the password). If we are able to find out what these nonces are, we are able to easily discover the wps pin, which finally leads to the cracking of passphrase. Here are the wonderful options of the Wi-Fi Hacker instrument that helps you crack a Wi-Fi network with a lot ease. WPA3 will likely be much tougher to assault due to its trendy key institution protocol known as “Simultaneous Authentication of Equals” (SAE).” Steube wrote in a submit. It still might take hours, but it’s a lot better than the previous state of affairs through which months of brute-forcing would yield no outcome. And that’s all of the combinations, and most likely the right pin won’t be the final mixture, so you may count on to reach the consequence earlier. BSSID of the network – Now irrespective of what you used, it is best to have a BSSID column within the end result that you simply get.
So, test the record of routers vulnerable to this attack accessible on google and cease utilizing WPS if your router is listed there. So, where is this taking us? So, they came up with a superb solution which no different password restoration device presents built-in at this second. Choose a file with “.cap”extension and kind the following command “aircrack-ng -w ” (aircrack-ng is a software that helps in cracking the password). If we are able to find out what these nonces are, we are able to easily discover the wps pin, which finally leads to the cracking of passphrase. Here are the wonderful options of the Wi-Fi Hacker instrument that helps you crack a Wi-Fi network with a lot ease. WPA3 will likely be much tougher to assault due to its trendy key institution protocol known as “Simultaneous Authentication of Equals” (SAE).” Steube wrote in a submit. It still might take hours, but it’s a lot better than the previous state of affairs through which months of brute-forcing would yield no outcome. And that’s all of the combinations, and most likely the right pin won’t be the final mixture, so you may count on to reach the consequence earlier. BSSID of the network – Now irrespective of what you used, it is best to have a BSSID column within the end result that you simply get.
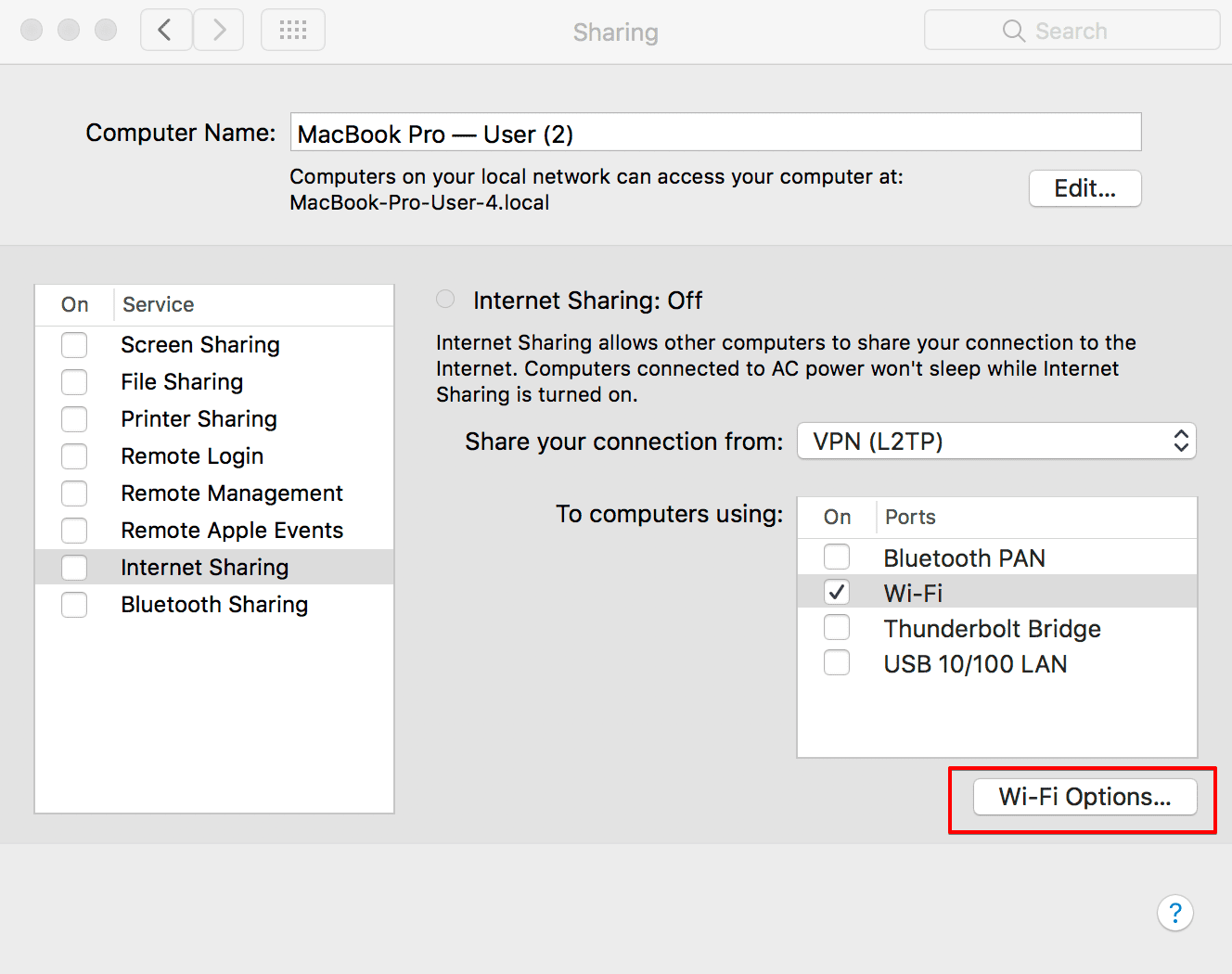
Does it have WPS enabled. If any network reveals up there, it has WPS enabled. The BSSID of the community. So by now you will need to have one thing like XX:XX:XX:XX:XX:XX, which is the BSSID of your goal community. Then click on the Scan button, this will scan for all the available networks all of the listed networks could have WPS setup. The brand new tactic solely works against WPA and WPA2-secured Wi-Fi networks with PMKID-based roaming features enabled. It tells which of them use WPA. Use wash (simple but typically unable to detect networks even when they have wps enabled). As is the case with all security standards, increasing pc power and uncovered vulnerabilities have rendered older Wi-Fi standards at risk. View your password from any Windows laptop that is already related to your community. Set your laptop to start from your USB drive by finding the “Boot Options” (or related) section, deciding on your USB drive’s title, and transferring it to the top of the record. A list of out there wireless networks displays.
4. Select the wireless with shopper, and click the launch to start out cracking process. When Wi-Fi was first developed within the late 1990s, Wired Equal Privacy was created to offer wireless communications confidentiality. A stroll by means of the historical past of Wi-Fi safety serves to focus on each what’s on the market right now and why it’s best to avoid older standards. The reply is, there are flaws on this technology that can be utilized towards it. Rainbow tables are recognized to hurry issues up, by finishing a part of the guessing job beforehand, but the output rainbow desk that must be downloaded from the net is disastrously large (will be 100s of GBs generally). Now hacking WPA/WPA2 is a very tedious job generally. And if you’re already accustomed to hacking WEP, then simply go to your Kali Linux terminal and sort the above command (replacing what needs to be replaced).