Learn How To Hack WiFi Utilizing Kali Linux, Crack WPA / WPA2-PSK Password
 To verify sort ls if there may be any file with the title of scan-01.Cap right here is the screenshot. Now, admittedly I’ve been up for some time so its fully possible that I am overlooking something fundamental and apparent, but when not, is there one thing you see that I’m doing unsuitable? If there may be wlan0 is present, then you may go forward. Client units within the transition mode will then connect with the rogue community utilizing WPA2, leaving the handshake exposed. For disconnecting the client from community monitor mode is essential (learn full submit you’ll perceive what I am talking about). The previous means of cracking WPA2 has been alongside quite some time and entails momentarily disconnecting a connected system from the entry point we wish to attempt to crack. Right now I need present you a special approach to cracking a password. Your search ends right here, here in the present day i’ll show you two strategies by which you’ll be able to hack wifi utilizing kali linux.
To verify sort ls if there may be any file with the title of scan-01.Cap right here is the screenshot. Now, admittedly I’ve been up for some time so its fully possible that I am overlooking something fundamental and apparent, but when not, is there one thing you see that I’m doing unsuitable? If there may be wlan0 is present, then you may go forward. Client units within the transition mode will then connect with the rogue community utilizing WPA2, leaving the handshake exposed. For disconnecting the client from community monitor mode is essential (learn full submit you’ll perceive what I am talking about). The previous means of cracking WPA2 has been alongside quite some time and entails momentarily disconnecting a connected system from the entry point we wish to attempt to crack. Right now I need present you a special approach to cracking a password. Your search ends right here, here in the present day i’ll show you two strategies by which you’ll be able to hack wifi utilizing kali linux.
In the present day we are going to study 5 Steps Wifi Hacking – Cracking WPA2 Password. In a pen tester’s life, eventually you are cracking a password. If you are not log in as the root person, then it’s going to ask for root password. In the event you already know then great. Step 2 — Utilizing the hcxpcaptool device, the output (in pcapng format) of the body can then be converted into a hash format accepted by Hashcat. Step-1: A hacker can use a instrument akin to hcxpcaptool to request the PMKID from the targeted entry level and dump the obtained body to a file. From the picture above, we are able to see many available entry level with all the information. Rather than counting on intercepting two-manner communications between Wi-Fi units to strive cracking the password, an attacker can talk straight with a susceptible access level using the new methodology. How Was The brand new Wi-Fi Hack Found? The best way to HACK WIFI PASSWORD. What we’re actually doing now could be waiting for a gadget to attach or reconnect to the network, forcing the router to ship out the 4-approach handshake that we have to capture with a view to crack the password.
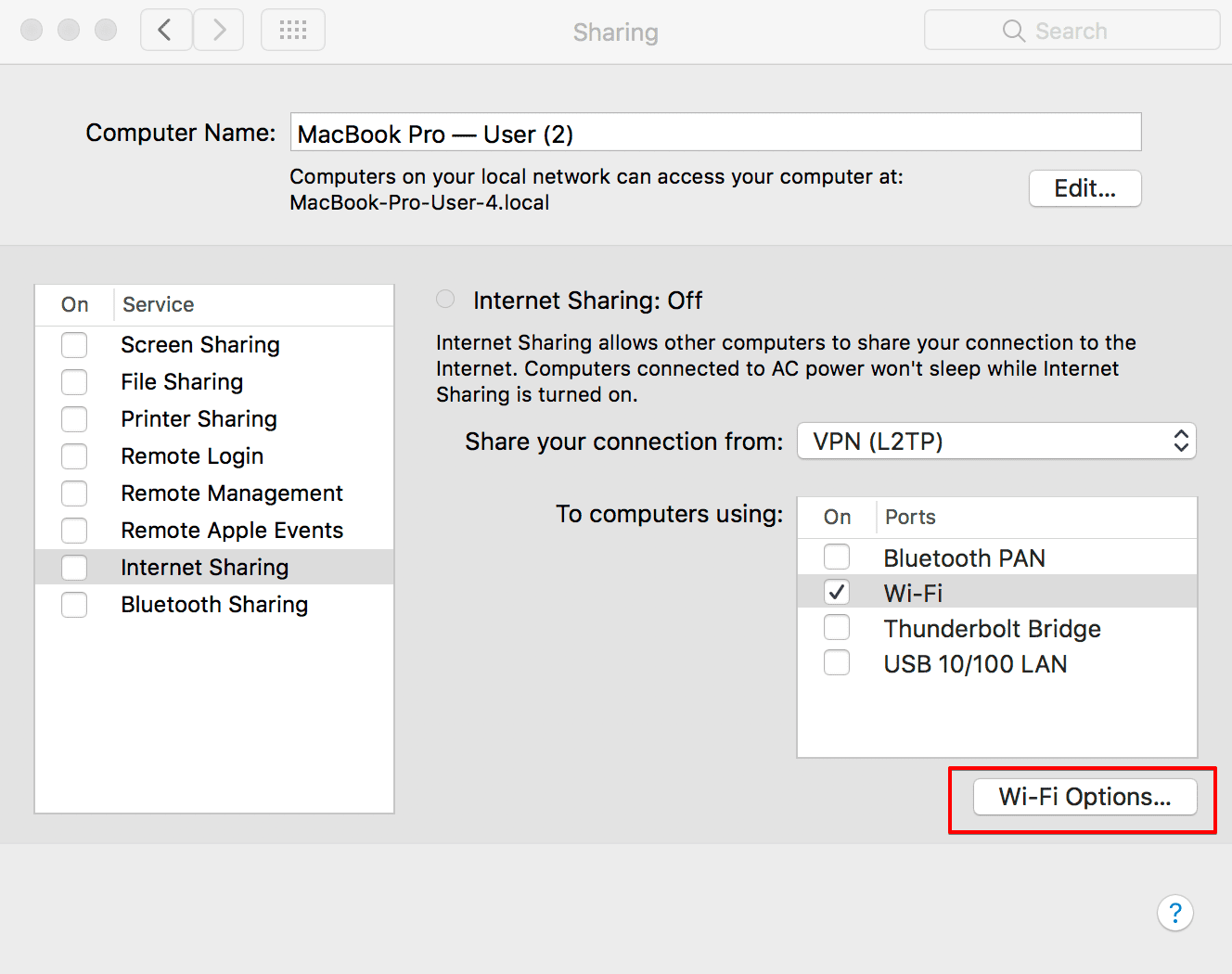
This can attempt to seize handshake imply wait till anyone isn’t becoming a member of your wifi (which makes no sense). 3. Click WiFi Setting from the left menu. Note – Before reading this weblog publish further, please be aware that hacking any wifi is unlawful. In line with the researcher, the previously recognized WiFi hacking methods require attackers to attend for someone to log right into a community and capture a full 4-method authentication handshake of EAPOL, which is a community port authentication protocol. The device you’re attempting to deauth might not be set to automatically reconnect, during which case you’ll either need to try one other gadget, or depart airodump on indefinitely until someone or something connects to the community. Now, you would possibly or may not get the warning appearing in the below screenshot which tells different processes using the network which may create the problem. Right here it’s wlan0, in your case it is likely to be different. This may almost certainly be your consequence too in opposition to any networks with a powerful password however expect to see outcomes here for networks using a weak password. A group of passwords and wordlists generally used for dictionary-attacks utilizing a wide range of password cracking tools similar to aircrack-ng, hydra and hashcat.
- Connect it by insert the password that you bought
- OclHashcat – A GPU-accelerated tool
- Run Dumpper as administrator, you may change language to English from the highest left tab
- Fast and extra reliable for any system
- 5 Steps Wifi Hacking – Cracking WPA2 Password
- Present the network password if it asks you and tap the connect button
This technique is used to generate an inventory of passwords with a sample IE all the passwords starting with a “1”. WPA2 passwords may be as much as 63 characters lengthy. I am certain that I’m inputting the right password (it is the WPA2 password written on the router; it’s not the wi-fi password itself), and it keeps getting rejected. The most generally-used Wi-Fi security protocol proper now continues to be Wi-Fi Protected Entry 2 (WPA2) encryption. In this system, nothing new identical software program Aircrack-ng and crunch Simply modified commands in the best manner. Proper after that we’ve to disconnect the entire connected wifi community from pc. It signifies that you should use wifi. Crunch generates all combination of eight characters, piping the outcomes to Pyrit that will use them to go through the attack to a .cap file. The WPA/WPA2 password list txt file can be used to hack wireless networks. We’ll create word listing text file utilizing crunch.